Hi,
We are now testing CTA+EOS, but have some problems with kerberos service authentication. Is kerberos essential for EOSCTA? Is there any way that we can avoid kerberos authentication?
Hi,
In our setup at CERN, we use SSS authentication between EOS and CTA. Kerberos authentication is used only for operators to run commands with cta-admin.
Until quite recently, Kerberos authentication was enforced for admin commands, but this constraint was removed on 1 December in v3.1-11. If you upgrade to the latest CTA version you can do without Kerberos completely.
OK, I just followed the steps on EOSCTA Docs. So the “CTA Frontend Kerberos Authentication” part in Configure CTA is not necessary, right? Is there any operation required to replace Kerberos authentication? Or is there some documents up to date?
At CERN we use SSS and Krb5. In theory any authentication mechanism supported by XRootD should work but we have not tested all possible configurations.
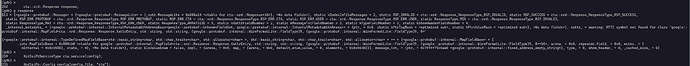
We now deployed CTA 3.1-13 and EOS 4.8.34 on 3 VMs, a Kerberos server, and created a service keytab for cta-frontend. Service like cta-taped, cta-frontend cta-rmcd, and Postgres look OK, but we encountered such error when we ran cta-admin drive ls:
Error from XRootD SSI Framework: [FATAL] Connection error
I made a simple debugging, and it seems that it goes wrong when executing
auto stream_future = cta_service.SendAsync(m_request, response);
in cmdline/CtaAdminCmd.cpp, and in the function SendAsync in xrootd-ssi-protobuf-interface/include/xrootd-ssi-protobuf-interface/include/XrdSsiPbServiceClientSide.hpp, the request doesn’t receive any data, throw an connection error exception, and exit.
I saw a similar problem in CTA/EOS-XrootD SSi Connection Error, but still, it does not work.
It goes wrong as above when executing cmd-admin v .
OK. I just made a stupid typo in the cta-cli config  . And now
. And now sss auth works for cta-admin, but kerberos still doesn’t work. I’ll do more on that.